More than Multi-Factor Authentication
December 12, 2019 •Jason Dell
Do you know Duo? Duo is Cisco's Multi-Factor Authentication (MFA) solution and It does a lot more than you might realize.
Phishing campaigns can be very convincing, even to the very discerning eye. Often hundreds, or even thousands of users are targeted in a phishing campaign.
It only takes one user to make a very human mistake and enter their credentials on a web page that looks very legitimate. Even if you have an aggressive password policy electronically enforced company-wide, it only takes one successful phish to permit cyber-criminals to have access to your critical business data assets.
How can Duo Help Mitigate a Phishing Attack?
Mitigating the risk of email-based phishing attacks is done with Cisco Email Security. Mitigating the risk of web-based phishing attacks is done with Cisco Umbrella. Mitigating the risk of these and other social engineering phishing attacks is done with user education.
But what if a user was phished, regardless? What can happen as a result? The attacker may be able to access the victim’s email or log into applications as the victim. They may even be able to remotely connect to the victim’s network and search for additional target systems to do additional malicious activity, like data exfiltration or malware installation. The consequences could be severe. Here’s how Duo can mitigate the impact of a phishing attack:
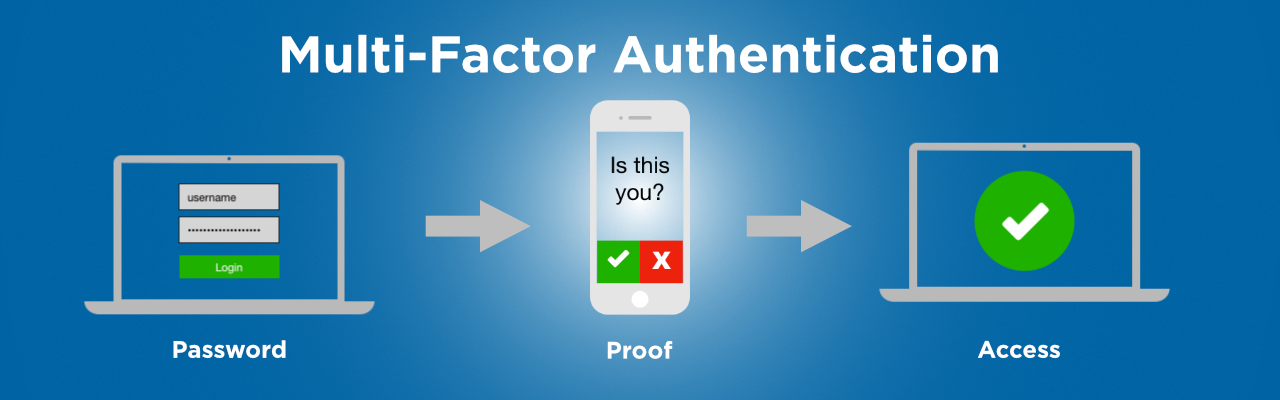
Multi-Factor Authentication
Duo provides multi-factor authentication for cloud applications, RADIUS-compatible services such as VPN, and even provides console access to systems such as Windows, MacOS, and Linux. Even if a user’s credentials are compromised, an attacker would not be able to approve the second factor of authentication.
Push Authentication
Duo securely “pushes” an authorization request to a mobile device running the Duo Mobile app. Push authentication is more secure then SMS (cellular text) or time-based one-time codes, both of which are subject to compromise. Your users don’t have mobile devices? Duo MFA also works with hardware tokens.
Mobile Device Posture Assessment
Duo offers posture assessment as well. You can set policy so that only certain mobile device manufacturers with certain OS versions are permitted to be used for push authentication. You can also set policy so that only compliant devices, OS versions, and/or browsers are permitted to be used for Duo’s browser-based authentication prompt.
Remote Access VPN
Duo can prevent attackers from connecting to your network via remote-access VPN. Duo provides native support to a number of remote-access VPN platforms, as well as generic RADIUS support for any other compatible remote-access platforms. See here to for a list of remote-access platforms that Duo natively integrates with: https://duo.com/docs#remote-access-and-vpn.
Applications
Duo integrates natively with several web and cloud applications to provide protection of your applications that are accessed on-site or by remote users. See https://duo.com/docs#microsoft, https://duo.com/docs#web, and https://duo.com/docs#identity-providers for an extensive list.
Single Sign-On
If you want to reduce the number of passwords that your users have to memorize, consider using Duo Single Sign On. Duo SSO works natively with a very large number of cloud applications, and with any SAML2 application. Have a look here https://duo.com/docs#cloud-service-providers to see some of the applications that Duo SSO integrates with.
Seeing is Believing
Need to see Duo in action? Visit https://demo.duo.com for an interactive demonstration of several Duo functions.
As well, NSI can provide a Duo trial for up to a month!
Schedule your Duo Trial!
Visit https://www.nsi1.com/scheduleconsultation to schedule a Duo trial or request anything else!
or
Contact your NSI account manager, or call NSI at 800-247-0900 to see a demo, for more information, or to get a quote.
Get Updates
Featured Articles
Categories
- AI (22)
- Automated Technology (12)
- backup (1)
- CAM (1)
- Cisco (34)
- Cisco Live Update (1)
- Cisco News (2)
- Cisco UCS (1)
- Cloud Networking (6)
- Collaboration (26)
- compute (1)
- CyberSecurity (38)
- Data Center (36)
- Defense (1)
- DevOps (3)
- DisasterRecovery (1)
- DNA (2)
- Education (3)
- Encryption (1)
- Enterprise Networking (39)
- Full-Stack (1)
- Future (1)
- healthcare (2)
- hybrid cloud (1)
- Hybrid Cloud Strategy (1)
- Hyperconverged Infrastructure (2)
- Infrastructure Cost Optimization (1)
- Innovation (1)
- Innovative Technology (12)
- Internet of Things (3)
- IoT (3)
- Managed Services (11)
- Manufacturing (2)
- Modern Data Center (2)
- Monitoring (3)
- Network Management (6)
- Networking (3)
- NSI (1)
- nutanix (1)
- Observability (2)
- OT (2)
- Ransomware (2)
- SchoolTechnology (6)
- SD-WAN (1)
- SDN (1)
- securit (1)
- Security (84)
- security management (12)
- security strategy (10)
- SmartHome (1)
- Software Defined Network (1)
- SSE (2)
- sustainability (1)
- Technology (1)
- Telehealth (4)
- Telemedicine (1)
- veeam (1)
- Video (1)
- videoconferencing (1)
- Virtualization (2)
- VMware to Nutanix (2)
- webex (3)
- wifi (2)
- XDR (1)
- Zero Trust (11)


